The ____ Commercial Site Focuses on Current Security Tool Resources
ECommerce is B2B and B2C online sales. Dominos 3 Carryout Tips TV Spot Transformation.
NIST develops cybersecurity standards guidelines best practices and other resources to meet the needs of US.
. Certain parts of a Windows PC are well on the way to hold data identifying with the malware installation and. It supports managers in making informed resource allocation tooling and security control implementation decisions. Liberty Mutual TV Spot Bad Job.
Security processes methods tools and techniques C. Operations and Incident Response Covering organizational security assessment and incident response procedures such as basic threat detection risk mitigation techniques security controls and basic digital forensics. Founded in 1957.
The Things That Matter Song by The Emotions. Firewall rule sets network defaults and intrusion detection system IDS settings D. A Nmap-hackers B Packet Storm C Security Focus.
In 2021 global commercial aircraft deliveries are estimated at 950 aircraft a decline of 41 from 2018 the peak year for deliveries7 Though the commercial aircraft order backlog stood firm at about 13421 at the end of December 2020 it was down 87 from the peak backlogs of about 14700 at the end of 20188 Apart from commercial. Another excellent resource that makes use of community resource mapping devoting much attention to the process of asset identification as well as to technique. Even a business with one computer or one credit card terminal can benefit from this important tool.
Here are tools and resources to help facility managers building owners tenants and other stakeholders improve waste management in their buildings reduce costs and enhance sustainability. By providing good ideas and customized solutions we focus on consistently delivering meaningful value even as. Removable media such as USBs CDs and so on are a useful tool for cybercriminals since they enable malware to bypass an organizations network-based security defenses.
Search Currents Document Library for spec sheets guides brochures design files and more for all of our lighting and controls solutions. Critical infrastructure vulnerability assessments are the foundation of the National Infrastructure Protection Plans risk-based implementation of protective programs designed to prevent deter and mitigate the risk of a terrorist attack while enabling timely efficient response and restoration in an all-hazards post-event situation. Configuration Item A hardware or software item that is to be modified and revised throughout its life cycle.
Start studying Chapter 12. The _____ commercial site focuses on current security tool resources. Our activities range from producing specific information that organizations can put into practice immediately to longer-term research that anticipates advances in technologies and.
Identifying Mapping and Mobilizing Our Assets. The tool is designed for businesses that lack the resources to hire dedicated staff to protect their business information and customers from cyber threats. The _____ commercial site focuses on current security tool resources.
The online advertising that leads to a sale. The point when performing a malware crime scene investigation. The sale through a website.
ECommerce has become a term that covers everything a business does online to sell to consumers both domestically and overseas. The PRIMARY objective of security awareness is to. The _____ mailing list includes announcements and discussion of a.
National security systems with a focus on the Defense Industrial Base and the improvement of US. True Rehearsal adds value by exercising the procedures identifying shortcomings and providing security personnel the opportunity to improve the security plan before it is needed. The _____ commercial site focuses on current security tool resources.
Apple TV TV Spot Pachinko. Configuration An __________ item is a hardware or software item that is to. This is mainly due to the fact that current security measures are not intended to deal with more complex threats 2012 Data Breach Investigations Report Verizon 2012.
Malware can be installed on the media and configured to execute automatically with Autorun or have an enticing filename to trick employees into clicking. Target TV Spot What We Value Most. Learn vocabulary terms and more with flashcards games and other study tools.
Guardian Alarm a Midwest residential and commercial fire security and automation systems provider is proud to announce the acquisition of Sievers Security in Cleveland Ohio. Expanded to focus on administering identity access management PKI basic cryptography wireless and end-to-end security. The _____ commercial site focuses on current security tool resources.
Progressive TV Spot Dr. Office buildings schools stores hotels restaurants and other commercial and institutional buildings generate significant amounts of materials and waste. It also strives to promote cybersecurity education research and career-building.
Budget estimates to acquire specific security tools 14. It also focuses on preventing application security defects and vulnerabilities. President Biden has made cybersecurity a critical element of the Department of Homeland Securitys DHS mission a top priority for the Biden-Harris Administration at all levels of government.
Commercial site focuses on current security tool resources. Mailing list includes announcements and discussion of a leading open-source IDPS. For more information about Security Systems please visit the Security Protection Category page.
Carrying out a risk assessment allows an organization to view the application portfolio holisticallyfrom an attackers perspective. At Santander Commercial Banking we are committed to earning our clients lasting loyalty by combining deep industry and capital markets expertise with global capabilities to help our clients prosper. NSA Cybersecurity prevents and eradicates threats to US.
To advance the Presidents commitment and to reflect that enhancing the nations cybersecurity resilience is a top priority for. For a complete list of the available offerings under MAS please view the Available Offerings Attachment on the GSA Available Offerings and Requirements page. Industry federal agencies and the broader public.
We generally recommend that businesses using more sophisticated. The brand building that helps tie it all together as a narrative for consumers. Improving Secondary Education and Transition for Youth with Disabilities prepared by Kelli Crane and Marianne Mooney.
Ensure that security policies are read and understood. Samsung Galaxy S22 S22 TV Spot Make Nights Epic Song by Wilson Pickett.

Practical Guide To Implement Surveys On Ict Use In Primary And Secondary Schools
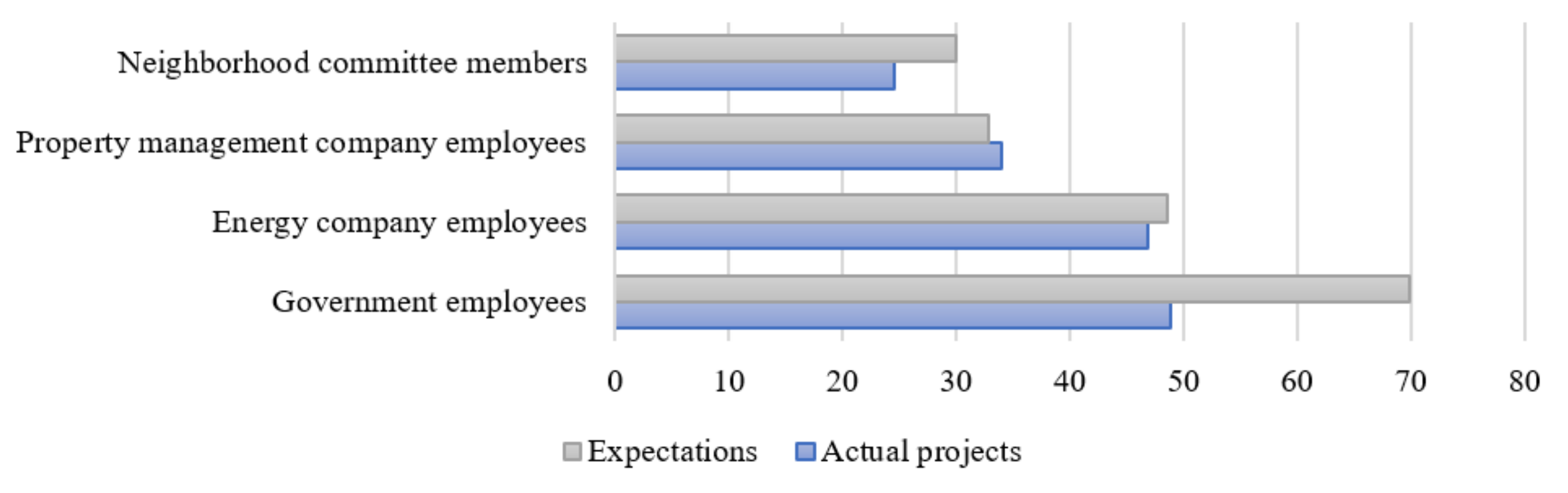
Sustainability Free Full Text Homeowners Participation In Energy Efficient Renovation Projects In China S Northern Heating Region Html
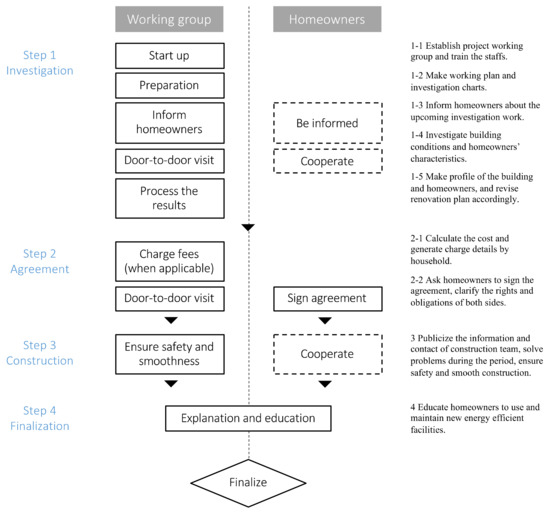
Sustainability Free Full Text Homeowners Participation In Energy Efficient Renovation Projects In China S Northern Heating Region Html

Brainly Review For Teachers Common Sense Education

Pdf A Comparative Study Based Digital Forensic Tool Complete Automated Tool

S 1 1 Tm215661d4 S1 Htm Form S 1 As
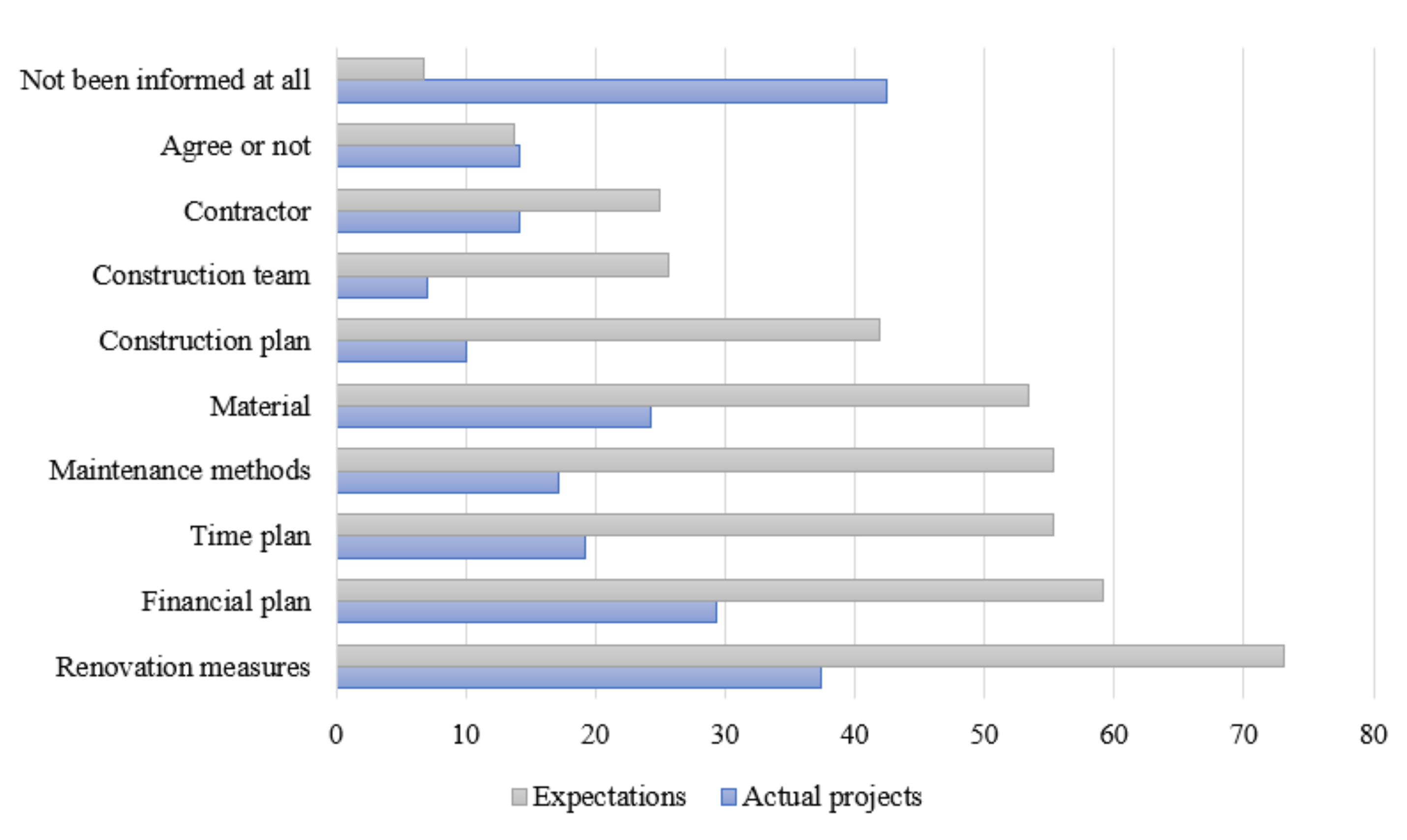
Sustainability Free Full Text Homeowners Participation In Energy Efficient Renovation Projects In China S Northern Heating Region Html

S 1 1 Tm215661d4 S1 Htm Form S 1 As
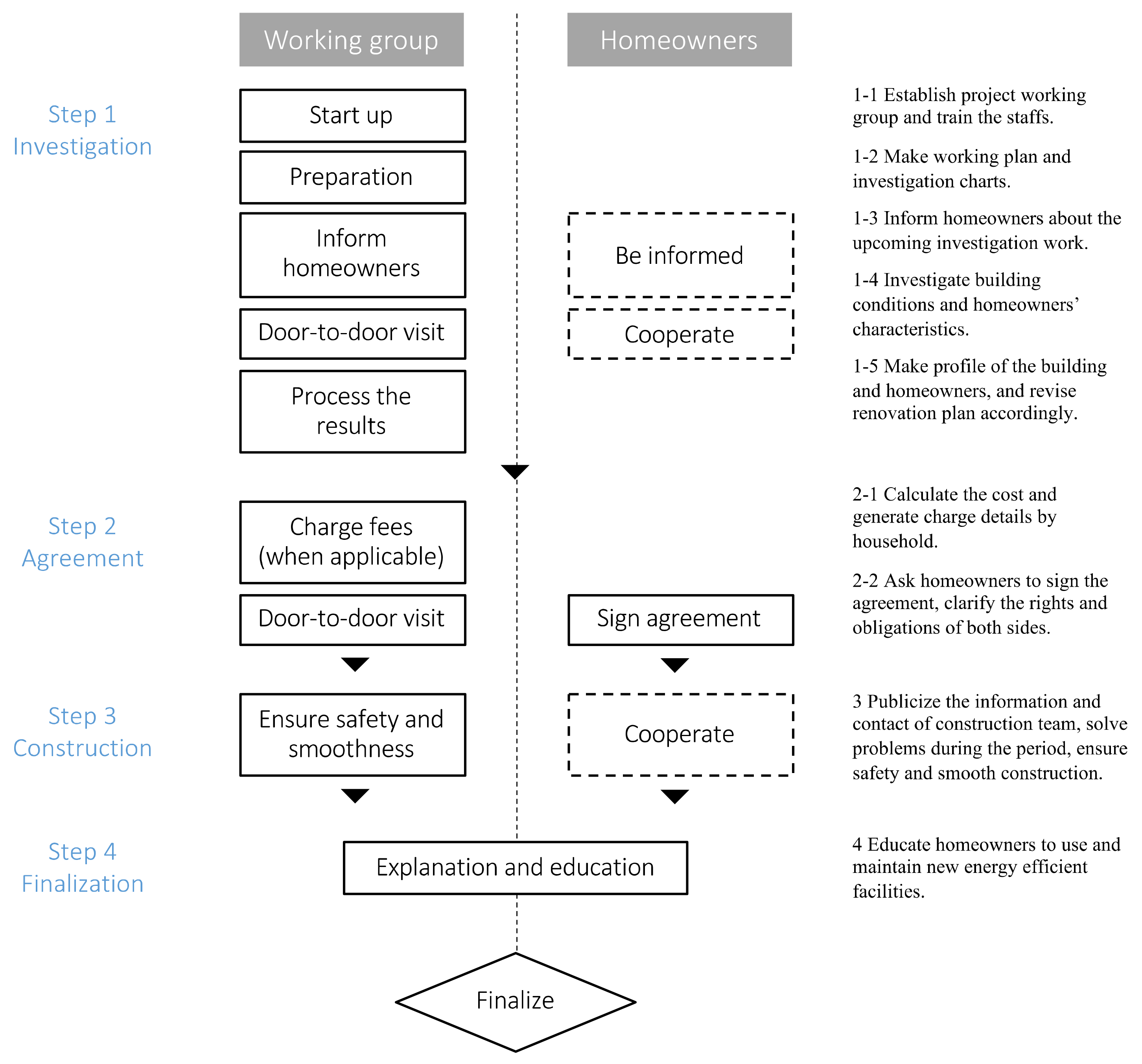
Sustainability Free Full Text Homeowners Participation In Energy Efficient Renovation Projects In China S Northern Heating Region Html

Combating The Conspiracy Of Silence Clinician Recommendations For Talking About Racism Related Events With Youth Of Color Journal Of The American Academy Of Child Adolescent Psychiatry
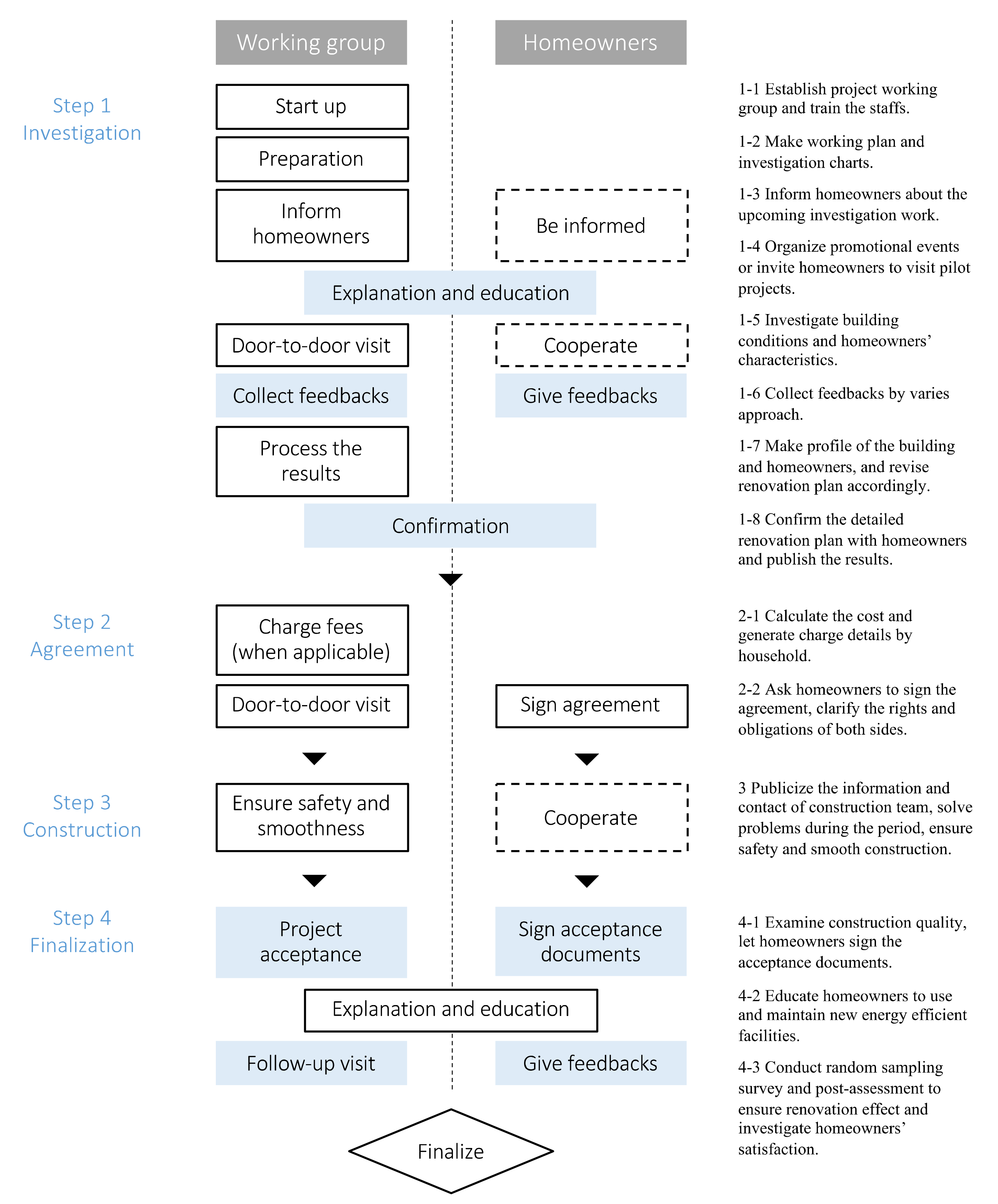
Sustainability Free Full Text Homeowners Participation In Energy Efficient Renovation Projects In China S Northern Heating Region Html
Pdf Beyond The Father And Family A Feminist Ethnographic Study On Early Marriage Decision Making Women S Empowerment And Gender Equality In Rural Pakistan

Pdf Software Testing Review On Tool Techniques And Challenges
Comments
Post a Comment